Welcome Mark Rodee, WSU's CISO
The Chief Information Security Office, or CISO, is a new position at Wichita State. The CISO stands outside of the ITS structure and reports directly to the Provost. The CISO’s responsibilities include providing leadership and guidance for the university’s efforts to comply with security standards and protect our critical data and intellectual property.
Mark Rodee has spent the 20 years in Information Security/Information Technology as part of leading high-tech manufacturing, communications test and defense companies. This includes being on the forefront of Information Security (InfoSec) practices as part of a new and growing industry including work in governance risk and compliance, incident response and security architecture. He is certified with ISC2, CISSP and SANS Institute, GIAC Security Leadership.
Mark has been with the university since early this year, and he is already making a big impact, helping shape top-level decisions that will influence the work we do every day. But with a background in defense industry work, what made him interested in working at Wichita State?
“God, family and country plays a big role in my life,” says Rodee, “and I realized that I was not investing locally as I worked remote. I wanted the next journey to be one where the products of my labor are a lifelong benefit to others.”
Over the coming months and years, Rodee will be working to update the university’s
security processes and practices. “What is the joy of life without a challenge?”
Rodee is looking forward to working with people across campus, and his door is always open. “If you have any questions over cyber security compliance, reach out. Compliance can be a costly roadblock, or it can build trust with our partners and enable business. We want to work with you to secure the important research and work done at WSU in order to continue having a safe computing environment”
If you would like to connect with Rodee and his team, you can reach out to Askinfosec@wichita.edu.

Avoid the scams of the moment
Chris Cavanaugh, the university's Chief Audit Executive, has been warning the university community about Coronavirus scams through WSU Audit Update, his most excellent blog. You can subscribe to his blog by sending him at email at chris.cavanaugh@wichita.edu. Here are few things to look out for according to Chris:
- Email and phishing scams disguised as messages from the CDC or WHO. Remember, these organizations are not going to ask you for information or to download content.
- Investment scams for fake treatment products.
- Fundraising for fake charities. Here's an article from the AARP to help you identify charity fraud.
- Illegal price gouging on safety or treatment products. The State of Kansas wants to remind you that the State Price Gouging Law is in Effect.
To protect yourself from scams, be very careful not to click on links from sources you do not know, and be sure all links actually direct you where they say they will. To check the "real" link, mouse over the hyperlink in an email or website: the actual destination will show up on your cursor or in the lower-left of your screen.
Also, be especially wary of emails claiming to be from the CDC or WHO, and simply ignore online offers for Coronavirus cures or investment opportunities. There are many Coronavirus scams out there, so be on your guard.
Don't get human hacked!
Social Engineering is not a degree we offer at Wichita State. Instead, "social engineering" is the formal name for the idea of "human hacking." Human beings always present a security challenge in any digital setting. Why? Because humans have empathy, get scared, and sometimes just don't know the right way to protect themselves. But you can protect yourself from human hacking with a few important habits:
- Don't take Facebook and other social media quizzes. Many social media quizzes ask you for all kinds of "fun" details. Want to figure out your samurai name? Tell me the street you grew up on and the name of your favorite pet! It's no coincidence that both of these pieces of information are answers to security questions that systems use to keep you safe. When you fill out social media quizzes, you risk handing a key to your security to the bad guys.
- Don't accept free "thumb drives" or ever put a thumb drive you have found into your computer. Thumb drives can be pre-loaded with viruses and spyware. Only use thumb drives from reputable retailers.
- Be careful with your personal and login information. One common way to harvest login
information is to "spoof" a website you are familiar with and then send out emails
with links to the fake website. The logos and layout may look just right, but if you
did not get there through your normal avenues (your bookmarked websites for example)
do not trust that you are in the right place. In doubt? Don't put in your personal
information. All reputable websites will have an updated SSL certificate, indicated
by a little lock icon in your browser's address bar:

- Report bad actors immediately. If you receive something suspicious on your Wichita State email, you can forward it to spamreport@wichita.edu for further investigation.
- Check your knowledge and habits by taking Google's Phishing Quiz. Good luck; it's hard!
If you think you have been hacked, there are a few things to do. First, if you put one of your passwords into a site you now believe to be disreputable, you should change it right away. If it happens to be the same password you use for multiple accounts, change the password on all of those accounts, and make each new password different. You should also consider running a virus scan on your computer, and finally, check your Outlook account for unusual "rules." This last tip comes from real experience at Wichita State: when some employees gave up their passwords in a phishing attack, ITS discovered the attackers had added unusual email routing rules to the employees' accounts. To check your rules on a PC go to the Home tab > Rules > Manage Rules and Alerts. On a Mac go to Home tab > Rules > Edit Rules. Make sure any rules you find are ones that look familiar to you!
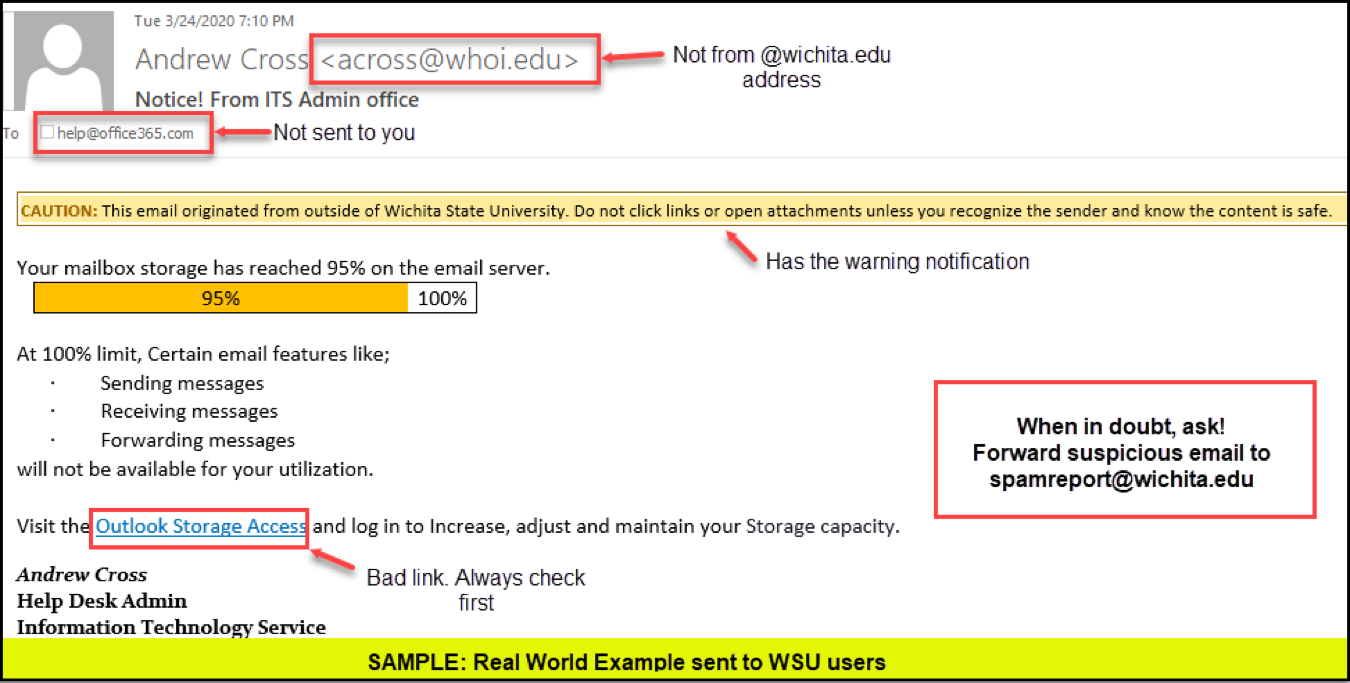
Don't become a phish story
Phishing has increased due to the COVID-19 pandemic. Don't get caught; know the signs as illustrated by this real phishing email. If you are in doubt, ask by sending the email on to spamreport@wichita.edu. Have questions about information security? Email askinfosec@wichita.edu:
Better living through updates
It's straight-talk time. Your computer's protections are only effective if they are updated regularly. If you avoid updates because you don't like changes in the way your software looks or behaves, you may be exposing yourself, your files, and your system to serious risk. It's time to get into the updating habit, but keep in mind if any updating options are grayed out for you on a Wichita State device, it is because ITS is keeping it updated for you. Here's what you need to check:
- On a PC (any computer that isn't a Mac): select the Start (window icon) button, and then go to Settings (gear icon) > Update & Security (arrow circle icon) > Windows Update (arrow circle icon). This will start a scan and possible update of Windows, which is your computer's operating system.
- On a PC, once it is updated: your PC has its own built in security program called Windows Security. Windows Security is always working to protect you with regular scanning. If you would like to run a manual scan of your system, something you should do if you have any reason to worry, Start > Settings (window icon)> Update & Security (lock icon) > Windows Security (shield icon) and then Virus & threat protection. You can choose a "quick scan" or "run a new advanced scan" and then "full scan" to check files and programs or "Windows Defender Offline scan" if you believe you may have a virus.
- On a Mac: click the apple icon in the upper left of your screen and choose System Preferences, and then choose Software Update. Your system will automatically scan to ensure you have the most updated version of your operating system. Make sure you check Automatically keep my Mac up to date before you close out of this area.
- On a Mac: if your Mac is Wichita State property, it will have an antivirus program called
Sophos already installed. To ensure Sophos is installed, updated, and running properly,
look for a small shield icon with an S in the middle at the upper-right portion of
your screen:
 . Click that icon for information about the status of Sophos, and update if directed
to do so. You can also reach the Sophos app from your Applications folder. If your
Mac is personal property, you should create a Sophos account and download the software immediately.
. Click that icon for information about the status of Sophos, and update if directed
to do so. You can also reach the Sophos app from your Applications folder. If your
Mac is personal property, you should create a Sophos account and download the software immediately.
Layer your security, just like a cake
So you have updated your computer, and you are running the latest antivirus protection, you're good, right? Not so fast. Software protections are only as strong as the weakest link, and as we discussed above, the weakest link in any computer security plan is often the human component. Don't be your computer's worst enemy.
In order to ensure that your home and work computers are truly protected from the very real possibility of attack, you should take a layered approach to security. Just like a business must consider its people, processes, and technologies when it plans its digital security systems, you need to always think about how you, your habits, and your software are working together to keep your own systems safe. It is possible to protect your digital self, but in order to do so, you need to believe the threats are real and make a plan for improved security.
Avoid "Zoom-Bombing"
You’ve probably heard the horror stories – someone comes into a virtual meeting, class, or event, and disrupts the session with a variety of offensive material and behavior. And the sad truth is these are real events, that have happened to real people. And not just in other places, but here at Wichita State.
The good news is that the problem is easily avoidable if we take a few precautions.
- There are important security features (using passwords, using waiting rooms, etc.) that we can use to make sure we have control over who goes into our sessions. Learn more about how to set up these features on our Zoom security page.
- Some settings require the host to grant entry to the class and permissions to guests. If it's too much to juggle both teaching and Zoom monitoring, request a co-host to handle your Zoom session so that you can focus on the content and your message.
Zoom bombings are serious incidents. If something happens in one of your classes, please be sure to report it here so the university can track events and also so those impacted can be offered counseling services.
Privacy and Zoom
As of this post, the university has decided to continue to use Zoom after a careful risk assessment. The process considered the high cost of changing platforms (both in time and money), the fact that the risks inherent in Zoom are also inherent in other platforms, and that those risks can be mitigated with practices that we have already put in place. We must continue to be careful about how we use Zoom, and how we protect sensitive information.
The good news is those techniques are not difficult. For example, we can be careful about how we invite people to our Zoom sessions. If we use a public platform like Twitter or Facebook to invite people, lots of unintended people will see that invitation. Sometimes that kind of invitation is necessary for recruitment events and other public gatherings, but Zoom gives us options and tools for locking down the experience so that we can do our best to make sure only the intended messages are being shared.
At the same time, we be careful about what in our physical space may appear on camera or in screen sharing, and we can be careful about the content that we share in a large, open meeting. And just as we do in an email, we can be careful about links we click on. We can share only the apps we need to when we share our screens. And we can to think about more analog solutions, too (see “Your webcam is a window,” below)
Zoom also has functionality that will allow us to give permission for someone to take over our screen as part of a screen sharing session. This can be very useful in a remote support situations, but we need to only do this with someone we know and trust.
We are still responsible employees
As a large percentage of the world has shifted to working, going to school, and living at home, reports of domestic/intimate partner violence and other domestic crime have increased. Because many Wichita State classes are using video contact with students, it is possible that you may witness something disturbing happening in a student's home. If you witness violence or have reason to believe a student of yours is unsafe, you are a responsible employee and have an ongoing duty to report this to the university. You can find reporting forms online, or if you would like to reach out by phone, you can contact Institutional Equity and Compliance at (316) 978-3205.
Your webcam is a window, so put up some curtains!
The new reality of home-based work and school increases the likelihood that you now have a webcam somewhere in your house. Video conferencing has become an important way we all connect with our family, coworkers, and students. But as helpful as your webcam is for maintaining social connection, you need to remember one important thing about it. Your webcam is a window into your home.
Now, that's not necessarily a bad thing. You probably have a least a few physical windows too, and they aren't doing you harm. But it's also easy to remember that physical windows can allow people to see inside if they aren't properly covered. It doesn't take too many visits to the bathroom before it occurs to everyone to put curtains on the window by the shower!
But a webcam "window" can be a little easier to forget about. Remember: even though you can't look out through your webcam, other people can use it to look in! And it's even possible for hackers and other bad actors to use your webcam when you are unaware. Here are some things you can do to protect yourself:
- Put up some curtains: The FBI recommends you cover your webcam when it's not in use. Thankfully, that's very easy to do with something as handy as a sticky note. Or if you want something more permanent, consider buying a webcam cover.
- Pay attention to where your webcam is pointing. By sitting with your back to a wall when you are using your webcam, you can ensure you are not revealing unintended information such as the layout of your home to strangers. You also dramatically decrease the likelihood that a housemate will accidentally reveal too much about themselves to your class!
- Consider obscuring your background entirely. Both Zoom and Teams allow users to obscure their backgrounds. If you can't control where your webcam is pointing, you should consider these options.
Password managers lead the way
Are you using strong passwords? Are you keeping them safe, never writing them down on bits of paper or sharing them with friends or family? If not, then you are putting yourself at risk.
Passwords are there to protect us, but complex password rules combined with frequent password changes across multiple systems and devices can mean that circumstances encourage us to develop bad password habits. Maybe you change your password by just one number each time? You would not be alone.
That's where a password manager comes in to save the day. A password manager is a simple computer program that keeps all your passwords safe and encrypted. The only thing you need to remember is the single password that secures you password manager. If you have a PC, you can choose from a variety of password managers. PC Magazine compiled a list of their top picks for 2020, and any of these are likely to be a good choice for you. If you have a Mac, your system comes with a password manager already. The Mac Keychain can even manage passwords across all your Mac devices, so it's quite handy to use.
OneDrive saves the day
What would happen if the computer you are on right now were to crash, taking all your data with it? Do you have a backup plan? If you have taken the time to set up Microsoft OneDrive on your system, the answer is yes! Even if your computer crashes and never works again, you can retrieve your data without issue from any computer that can reach the internet.
OneDrive is nothing more exotic than an internet-based "hard drive" where you can store your work and personal files. As a Wichita State employee, you have access to this storage capacity through the Microsoft 365 suite of programs. There has never been a more important time to set up OneDrive and protect your data. You can learn about how to set up and access OneDrive through this ITS training page.
Secure your home network
When you are at work, you benefit from having a team of network security professionals looking out for your connection to the world. But when you are at home, the responsibility for your network's security falls to you. And that might sound a little scary if computers aren't your thing.
The good news is that you can do it! There are a few simple tasks for you to undertake that will keep you from being an easy target, and will even help protect you against a more sophisticated attack. Here is what you need to do:
- Get to know the terms. In many ways, the internet is like any other utility that comes into your home: the internet flows past your house through existing phone lines, special glass fiber, or some other conduit. You need to tap into that flow of information with a device, and that device is called a modem. Once your modem grabs the internet for you, you then need to distribute that connection inside your house. This is done with a device called a router. Your computer devices connect to the router. Most systems today have a single device that serves as both the modem and the router. When you "secure your network," you are making sure your modem, router, and connected devices are all safe from attack through the internet (inbound attacks), and you are also ensuring that your personal devices are not being used to attack the internet itself (outbound attacks).
- Understand how attacks happen. Network attacks happen when someone can get in through a "door" that has not been well secured. That can happen because someone outside your home, and perhaps very far away, exploits a weakness in your system, or it can happen because you make a poor choice that invites a bad actor access to your devices. Although people tend to understand and fear inbound attacks to their networks, outbound attacks, where your devices are used as bad actors on the internet, are actually more common.
- Do the things you can do. When your internet system was first installed, you were provided information about
your modem and router. In order to ensure proper security, you are going to need to
find that information. If you are lucky, it is printed directly on the router itself,
but if not, you may need to contact your internet service provider for information
about how to access your system. Contacting them is as easy as giving them a call
or logging in to your account online. Once you have access to your router, you should:
- Give your network a name that is different from the default code the system came with. This may have already been done when the system was set up, and if so you do not need to change it.
- Change the password to your router. This is an important step, and you need to know how to do it yourself. Your router has an administrator (admin) password that only you should know. Make it long and complex so it cannot possibly be guessed no matter how much personal information a hacker has about you.
- Change the password to your wifi. Get into the habit of changing your password on a schedule, and certainly after every time you have given it to a guest. Make sure your password is complex and not tied to your house; for example, using your street address is a bad idea.
- If available with your internet service, set up a guest login for your system. This keeps your guests from ever having your regular wifi password, and it keeps them off your main network.
- If you have to use an internet connection (perhaps from your phone) to change settings in your router, use a private ("incognito") browser window to access your system, and close out your browser entirely when you are finished making changes.
- Follow all the personal security tips contained in this newsletter. Remember, your network is only as secure as its weakest link. Accept that you will always be that weakest link, and work to have the best computer security habits possible.
Why not wifi?
Wifi is a modern convenience that few of us would want to live without. But sometimes, wifi is simply not the best way to connect to your network. There are two considerations you should think through before deciding to use wifi for a task:
- Are you on a secure wifi connection? Wifi security is different for your home network than it is out in the world. If you have taken precautions to secure your home network, then it should be sufficient for most computer tasks, although you may still want to use a cable connection for banking and other ultra-sensitive information. But if you are on a public wifi connection, such as at a coffee shop (remember those?), you should assume that you are on an insecure network, and anyone can access the data you are putting on the network. If you are simply not sure if the network you are using is secure, it's always best to "cable in" rather than trying to use wifi. If you don't have access to a cable and simply must get on the internet, then it is always more secure to use you smartphone's cellular data either directly or by making your phone a hotspot. Cellular connections may "feel" like wifi because they don't use a cable, but they are much more secure than an unsecured network would be.
- Does speed matter? A wifi connection will never be as fast or as robust as the connection you get by using a cable. If you are passing a lot of data back-and-forth (such as when you upload a video to YouTube) or if a steady connection is very important (such as when you are working in Blackboard or on Zoom), then it is always best to use a cable to connect to your network.
Why is this so slow...?
Those of you who remember the dawn of the Internet remember the joke: what does "www" stand for? World Wide Wait.
In the last several years, network speeds have gotten speedier, and if you are used to doing most of your internet surfing at work, you have gotten pretty spoiled. Speeds on campus are incredible!
Now that you are home and trying to upload and download across a neighborhood network, you have probably noticed that things have slowed way (way, way) down. Sometimes it's almost like the internet has stopped working entirely. At the same time, internet destinations (like Panopto and Zoom) that were set up to serve many fewer users are now taking much more use. Zoom, Blackboard, Panopto, and other university vendors are doing their best, but no one was ready for the surge in use.
So, what can you do, and how do you even know if an unusually slow work session is due to your network or the service you are trying to use? Here are a few tips:
- Get to know your network speeds. Using the free Speedtest tool provided by Ookla, get into the habit of running your numbers throughout the day. If you experience a significant slowdown, check again and see if your upload or download speeds have dropped off. If they have, wait awhile and try again later.
- Try uploading videos at off-peak hours. Very late at night and very early in the morning are both better times to put videos on YouTube and Panopto. You share your neighborhood network with your neighbors, so the fewer of them who are awake, the better.
- Check to see if the service you want to use is experiencing downtime. Here are a few links for commonly used services at Wichita State:
Do I have a virus?
Here's an interesting fact: a virus that makes you sick is not very different from a virus that makes your computer sick. Both types of virus are no more than a bit of information that "infects" a body and then causes harm. Computer viruses can be transmitted through physical contact (plugging in an infected thumb drive, for example) or through your network connection. Once your computer has a virus, it is likely to need some kind of treatment.
There are several common symptoms of computer viruses. You may notice significant loss of speed and performance, or you may see a sudden uptick in the number of popup ads that you are getting. You may also notice these popup ads are surprisingly ... graphic.
If you suspect you have a virus, the first thing to do is run your antivirus program. Whether you use Sophos or Windows Security, running a scan is as easy as opening the program and following the prompts. If it turns out that you do have a virus, don't be embarrassed. It happens to everyone eventually. It's possible your antivirus program perform a simple fix, but if the infection is serious, it will need intervention by a specialist. Always report any suspected infections on a Wichita State owned device to helpdesk@wichita.edu. Please do not try an clean a virus on your own as it could break other key services your machine needs to operate properly.
If you have to wait to have your computer fixed, it is critically important to disconnect it from the internet. Go ahead and unplug it too. Your goal is to keep the infection isolated to that one machine. Wichita State's Help Desk will assist you with getting work computers fixed. If it is a personal computer, you will need to take it to a "computer doctor" in town. If you need a loaner computer to do your job in the meantime, contact the Help Desk.
Helpdesk and Desktop Support
Sometimes it can be hard to know where to go with a computer problem. Happily, ITS makes things easy by taking all questions through the Technology Help Desk. You can reach the Help Desk online, or directly through an email to Helpdesk@wichita.edu. ITS also provides a guide to picking the right help option for different situations. If you would like to directly to the right place on your own, check out this handy guide to getting help.
IDA is on your side
Sometimes it can be hard to know if your "computer problem" is a problem with the computer itself or with the applications you are trying to run. If you are experiencing problems with Blackboard, Zoom, Panopto, or Respondus LockDown Browser, please reach out to Instructional Design and Access via email at IDA@wichita.edu. IDA has the training to know if your issue stems from a computer issue, and if so, they will let you know and loop the Help Desk in immediately. You don't need to worry if you are in the right place!